Unwanted Witness report exposes personal data misuse in the past election cycle
COVER STORY | RONALD MUSOKE | On May 12, President Yoweri Kaguta Museveni, 81, will take the oath of office once again, extending a presidency that has shaped Uganda’s political landscape for four straight decades. His victory in the Jan. 15 election, where he secured 71.65% of the vote, according to official results, has already been affirmed by the Electoral Commission, placing him comfortably ahead of his closest challenger, Robert Kyagulanyi Ssentamu, who received 24%.
President Museveni’s inauguration at Kololo Independence Grounds in Kampala, which according to the Uganda Media Centre, the government’s communications clearing house, will be held under the theme: “Protecting the Gains, Making a Qualitative Leap into High-Middle-Income Status,” is expected to draw in thousands of supporters and high-profile guests from around the world.
Museveni’s swearing-in will mark the end of another fractious election cycle in Uganda’s recent general election history. But beneath this sense of closure lies a quieter, unresolved story; one that did not play out on tally sheets or campaign stages, but within databases, mobile phones, and biometric devices. It is a story about how personal data shaped Uganda’s most technologically complex election to date, and how questions about that data remain unanswered even as the country prepares for inauguration.
Unsolicited campaign messages on the phone
In Kampala’s Kamwokya neighbourhood, the election still lives in the memory of a text message. Steven Ilakitari, a Boda Boda (motorcycle taxi) rider, recalls receiving campaign SMS texts on his Airtel and MTN mobile phone numbers, just days before Ugandans went to the polls. The messages arrived unprompted, bearing slogans associated with the ruling NRM party and urging him to vote for the incumbent.
“I was angry because I didn’t know where they had got my number from,” he told The Independent. Another rider, Charles, scrolls through his phone and finds the messages still saved. One of the SMS texts promises expanded Parish Development Model (PDM) funding, free education, and cheaper internet. Another urges calm participation on polling day, signed off with NRM party campaign branding. Neither man belongs to the NRM nor do they recall giving consent to receive such messages. Neither man knows how their contact details were obtained.
Their experience is not unusual. Across the country, millions of Ugandans, including this reporter, received similar communications; targeted, timely, and often personalized. Each message carried not only a political appeal, but an implicit question: who had access to this data, and under what authority? These questions sit at the centre of a new report by Unwanted Witness, a Kampala-based civil society organization that advocates for citizens’ digital rights including; the right to privacy, digital identity, digital inclusion, and freedom of expression. The report titled, “Uneven Enforcement of Data Protection Laws Puts Data Subjects’ Rights at Risk in Uganda’s 2026 Polls,” examines how personal data was governed during Uganda’s 2026 electoral cycle.
The architecture of a digital election
To understand the scale of the issue, it is necessary to look at how Uganda’s elections have evolved. Over the past decade, the country has transitioned from a largely paper-based electoral system to a hybrid model in which digital technologies are deeply embedded. During the 2026 general elections, this transformation reached a level of complexity that fundamentally altered how elections were conducted.
At the heart of this system was the nationwide deployment of 109,142 Biometric Voter Verification Kits (BVVKs). These devices were distributed across 50,739 polling stations, with each station equipped with both a primary and backup unit. Their use was no longer optional; under new regulations, biometric verification became a mandatory prerequisite for voting. No ballot could be issued without it.
Each BVVK was supposed to function as more than a simple identity-checking tool. It incorporated fingerprint scanners, facial recognition fallback systems, local copies of voter registers, and internal storage capable of logging verification events. Some units also supported scanning and digital archiving of result forms. In effect, each polling station became a node in a wider data network; collecting, processing, and storing sensitive personal information in real time.
Alongside this system was the integration of Uganda’s National Identification Number (NIN), managed by the National Identification and Registration Authority (NIRA), the government agency in charge of creating, managing, and operationalizing the national identification register. The NIN, the unique lifelong identifier of citizens, became the backbone of voter registration and verification, linking civil identity data directly to electoral participation. This convergence created a centralized ecosystem in which identity, eligibility, and participation were all mediated through interconnected databases.

Efficiency, risk, and the question of oversight
From an administrative perspective, these innovations were presented as necessary upgrades. Biometric verification promised to reduce voter fraud, eliminate duplicate registrations, and streamline the voting process. Integration with the national identity system was framed as a way to improve accuracy and efficiency. But as the Unwanted Witness report makes clear, these same features also introduced significant risks.
Biometric data including, fingerprints and facial images, is inherently sensitive. Unlike passwords or identification numbers, it cannot be changed if compromised. When combined with a centralized identity system like the NIN, it creates a powerful and potentially vulnerable dataset. Despite the high-risk nature of this processing, the report found no publicly available Data Protection Impact Assessments (DPIAs) for the biometric systems or the NIN integration.
Such assessments, the report notes, are typically required to evaluate risks and establish safeguards before large-scale data processing begins. Their absence leaves critical questions unanswered: How, for instance, is the data secured? Who has access to it? How long is it retained? And, under what conditions can it be shared?
When the machines falter
The promise of technology also collided with the realities of implementation. On polling day, nationwide reports emerged of BVVK failures across multiple locations. Some devices struggled to load voter data, others failed to authenticate fingerprints, and some did not function at all. With the whole country under an internet blockage, connectivity challenges and insufficient training compounded the problem, forcing election officials to revert to manual verification procedures.
These disruptions had immediate consequences. Voting was delayed, queues lengthened, and inconsistencies emerged in how verification was conducted. But they also raised deeper concerns about the integrity and auditability of the process. Biometric systems are often justified on the basis of their ability to produce reliable, verifiable records. When those systems fail, or when their logs are incomplete or inaccessible, the very safeguards they are meant to provide can be undermined.
Data beyond the polling station
While much attention focused on polling-day technology, the report highlights that personal data played an equally significant role outside the polling station. Digital voter verification portals allowed citizens to check their registration details online. These platforms, activated weeks ahead of the polls, were intended to enhance transparency and accessibility, enabling voters to confirm their polling locations and personal information. In practice, however, they also processed and displayed large volumes of personal data, including names, photographs, and registration details.

It is within this context that the FANON incident emerged. FANON, a civic-tech platform that gained traction during the electoral campaign period, allowed users to search for voter information with relative ease. Although its creators claimed the data was sourced from publicly displayed registers, the scale and functionality of the platform raised serious concerns.
The ability to search, aggregate, and potentially download voter data transformed what might have been individually accessible records into a centralized and highly valuable dataset. Even if each piece of information was technically public, its aggregation created new risks, particularly in a political environment where data can be used for profiling and targeted messaging. The incident exposed weaknesses in authentication controls, rate limiting, and overall system governance. It also highlighted the thin line between transparency and exposure in a digital system.
“The FANON incident illustrated how large datasets could potentially be scraped, aggregated, or repurposed, highlighting weaknesses in authentication controls, rate limiting, and system governance,” the report notes.
Campaigning in the age of data
If the state’s use of data reshaped electoral administration, political actors used data to reshape campaigning. The 2026 election saw an expansion of data-driven campaign strategies, including bulk SMS messaging, automated calls, and targeted advertising on platforms like WhatsApp, X, Snapchat, Instagram, Facebook, and TikTok. These methods allowed campaigns to reach voters, especially first-time voters directly, bypassing traditional media channels.
But they also depended on access to personal data; phone numbers, demographic information, and inferred political preferences. For observers, the key issue is not simply that such techniques were used, but how the underlying data was obtained.
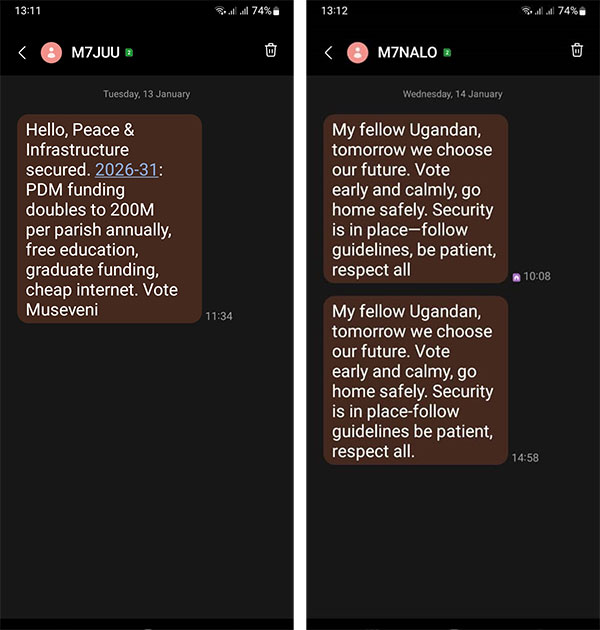
A Kampala-based lawyer who is familiar with data protection law frames the issue starkly: “Every unsolicited political SMS that reached a Ugandan phone during the 2026 campaign raised a question that neither the Electoral Commission, the Personal Data Protection Office, nor the major telecommunications operators have publicly answered: how did political parties obtain these numbers?”
Under Uganda’s legal framework, telecommunications data is collected for specific purposes and cannot be repurposed for political campaigning without a lawful basis and, in most cases, informed consent, the lawyer who preferred to speak on condition of anonymity, told The Independent.
Yet, as the lawyer notes, the accountability trail remains elusive: “What remains missing, cycle after cycle, is the accountability trail: the data-sharing agreements, the lawful basis documentation, the records of consent.” In the absence of such transparency, each message received by voters like Steven Ilakitari becomes part of a larger, unresolved puzzle.
Institutional responses and their limits
Faced with these concerns, the Electoral Commission has emphasized its commitment to compliance and continuous improvement.
Julius Mucunguzi, the Commission’s spokesperson, describes data protection as an ongoing priority. But when The Independent asked him to respond to the report’s findings; that the Commisison suddenly rushed to register with the Personal Data Protection Office in Kampala, just four days after declaring Museveni winner of the presidential election, Mucunguzi said: “The EC does its work according to work plans and is guided by its strategic direction.”
He added: It is the commitment of the EC to be law-abiding and compliant with all processes and procedures.” He acknowledges the importance of registration with the Personal Data Protection Office, even if it occurred after the election: “The electoral processes are not ending tomorrow; there will be other elections after the general elections. It’s still very important for the EC to register with the PDPO because the management of elections in Uganda is still the EC’s mandate for both present and future elections.” For the Commission, the issue is framed as part of an evolving institutional process.
“At whatever point a good practice emerges, the Commission should embrace it,”Mucunguzi told The Independent.
A systemic gap
For Unwanted Witness, however, the issue is more structural. Allan Ssempala Kigozi, the Head Legal and Programmes, argues that the core problem lies in the gap between legal frameworks and their implementation. “What is most striking is not the absence of a legal framework; Uganda has one, but the systematic failure to implement it where it matters most,” he said.
He points to what he describes as institutional non-compliance at the highest levels. “The Electoral Commission only registered with the Personal Data Protection Office after the elections (January 21, 2026)… At the same time, no political party registered at all, yet they actively engaged in bulk SMS campaigns, phone outreach, and voter profiling,” he said.
This, he suggests, creates a broader issue of consistency and fairness: “While ordinary individuals faced enforcement actions under digital laws, major institutional actors handling large-scale personal data operated outside compliance,” Kigozi said. The result, Kigozi added, is what the report terms an “implementation deficit,” a situation in which laws exist but are not effectively enforced.
Data, trust, and democratic legitimacy
Beyond the technical details, the report situates data protection within a larger democratic context. The report notes that elections depend not only on accurate vote counting, but on public confidence in the system. When voters are uncertain about how their data is used, or fear it could be misused, their trust in the process may be affected.
The integration of biometric systems, national identity databases, and digital campaigning tools has raised the stakes. A breach, misuse, or lack of transparency in any part of this system can have far-reaching implications. In this sense, data protection is not a peripheral issue. It is central to how elections are experienced and perceived.
Going forward, Unwanted Witness says the priority should move from reactive compliance to embedded, proactive data governance. Specifically for the Electoral Commission, it must institutionalize data protection as part of election planning, not as an afterthought.
This includes publishing a clear Electoral Data Governance Framework covering how voter data is collected, used, shared, and deleted. “It should conduct and publish DPIAs for all high-risk systems, especially biometric verification and NIN integration and there is also a need for independent cybersecurity and data audits before elections, to ensure systems are secure and trustworthy,” Kigozi said.
For political parties, they must recognize that they are data controllers and comply accordingly. This should start with mandatory registration with the PDPO several months before elections.
“They should adopt transparent consent-based campaigning, particularly for bulk SMS, phone calls, and digital targeting,” Kigozi told The Independent, adding that, “The use of analytics, profiling, and AI tools should be subjected to data protection impact assessments and ethical safeguards.”

As, for the Personal Data Protection Office (PDPO), it should shift from reactive enforcement to proactive oversight, including issuing clear, election-specific guidelines well in advance of the electoral cycle. “It should also establish a dedicated electoral data oversight mechanism during election periods.”
For Parliament, Unwanted Witness says, there is need to explicitly embed data protection obligations into electoral laws, including mandatory audits, retention limits, and clear rules on data sharing between agencies like EC and NIRA.
“The bottom line is that as elections become more digital, data protection is no longer a technical issue, it is central to electoral integrity. If left unaddressed, these gaps risk undermining voter trust, enabling manipulation, and weakening the legitimacy of democratic outcomes,” Kigozi added.
Looking beyond May 12
Now, as Ugandans prepare for the swearing-in, the official narrative of the election is one of completion. The process has run its course, the winner has been declared, and the next phase of governance is about to begin. But the data story does not end there.
The systems deployed in 2026; biometric verification, NIN integration, digital campaigning, are likely to remain in place, shaping future elections, with the closest one expected to be 2031 unless electoral laws are amended to reduce or increase terms of office for the elected leaders. The questions raised by this cycle will carry forward unless they are addressed.
For voters like Ilakitari, the issue is more immediate. The messages he received may have been just a few lines of text, but they pointed to something larger, a system in which personal data moves in ways that is not always visible or understood. As the country marks another inauguration of Museveni, that system remains in place. And so do the questions it raises.
 The Independent Uganda: You get the Truth we Pay the Price
The Independent Uganda: You get the Truth we Pay the Price